In Part 2 we will script a PowerShell file and execute it. It is a very simple example. However there are a few preliminary things you should be aware of.
Launch Windows PowerShell in Windows 8.1
Launching Windows PowerShell in Windows 8.1 is easy. Windows 8.1 comes with PowerShell. Click the Search charm and type in 'Windows PowerShell' or, in the all apps, pick Windows PowerShell and click.
The Windows host launches the Windows PowerShell as shown.
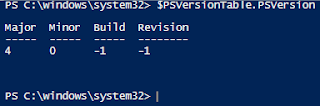
You type in the command $PSVersionTable.psversion to get the version on your computer as shown. It will be probably version 4.0.
------------
Now let us create a file, a simple one and save it with the extension ps1. I will show you later what this file look like. Launch Windows PowerShell in Windows 8.1
Launching Windows PowerShell in Windows 8.1 is easy. Windows 8.1 comes with PowerShell. Click the Search charm and type in 'Windows PowerShell' or, in the all apps, pick Windows PowerShell and click.
The Windows host launches the Windows PowerShell as shown.
You type in the command $PSVersionTable.psversion to get the version on your computer as shown. It will be probably version 4.0.
------------
However to run a script file you need to know about the execution policy. You can get a good handle on this here:
http://technet.microsoft.com/library/hh847748.aspx
How do you know what policy is in force?
To see the policy in force, just type the commandlet Get-Policy as shown and you get an immediate answer.
====
PS C:\Users\Jayaram\Desktop> Get-ExecutionPolicy
Restricted
PS C:\Users\Jayaram\Desktop>
======
'Restricted' is the default policy in Window 8, Windows 8.1 and Windows Server 2012
What does 'Restricted' mean to you?
- Permits individual commands, but will not run
scripts.
- Prevents running of all script files, including
formatting and configuration files (.ps1xml), module
script files (.psm1), and Windows PowerShell
profiles (.ps1).
Well, you see with 'Restricted' policy enforced, you cannot run a script file (I created one called Hello.ps1 and tried to run with default policy). Actually Power Shell tells you this, if you try to run one as shown,
=====
.\Hello.ps1 : File C:\Users\Jayaram\DEsktop\Hello.ps1 cannot be loaded because running scripts is disabled on this
system. For more information, see about_Execution_Policies at http://go.microsoft.com/fwlink/?LinkID=135170.
At line:1 char:1
+ .\Hello.ps1
+ ~~~~~~~~~~~
+ CategoryInfo : SecurityError: (:) [], PSSecurityException
+ FullyQualifiedErrorId : UnauthorizedAccess
====
OK. How do you change this policy?
Well, you need the policy changed to 'Remote signed'.
What does 'Remote Signed' mean to you?
It means,
- Scripts can run. This is the default execution
policy in Windows Server 2012 R2.
- Requires a digital signature from a trusted
publisher on scripts and configuration files that
are downloaded from the Internet (including
e-mail and instant messaging programs).
- Does not require digital signatures on scripts that
you have written on the local computer (not
downloaded from the Internet).
- Runs scripts that are downloaded from the Internet
and not signed, if the scripts are unblocked, such
as by using the Unblock-File cmdlet.
- Risks running unsigned scripts from sources other
than the Internet and signed, but malicious, scripts.
How do we change the execution policy?
Well, Power Shell has this "Set-ExecutionPolicy" command. The syntax is:
Set-ExecutionPolicy -ExecutionPolicy RemoteSigned
There is one more thing you need to take care of before you change the policy and that is, you should run the command with elevated permissions (you should run the script as an Administrator of the local machine). If you do not ,you will get this exception:
================
PS C:\Users\Jayaram\DEsktop> Set-ExecutionPolicy -ExecutionPolicy RemoteSigned
Execution Policy Change
The execution policy helps protect you from scripts that you do not trust. Changing the execution policy might expose
you to the security risks described in the about_Execution_Policies help topic at
http://go.microsoft.com/fwlink/?LinkID=135170. Do you want to change the execution policy?
[Y] Yes [N] No [S] Suspend [?] Help (default is "Y"): y
Set-ExecutionPolicy : Access to the registry key
'HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PowerShell\1\ShellIds\Microsoft.PowerShell' is denied. To change the execution
policy for the default (LocalMachine) scope, start Windows PowerShell with the "Run as administrator" option. To
change the execution policy for the current user, run "Set-ExecutionPolicy -Scope CurrentUser".
At line:1 char:1
+ Set-ExecutionPolicy -ExecutionPolicy RemoteSigned
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : PermissionDenied: (:) [Set-ExecutionPolicy], UnauthorizedAccessException
+ FullyQualifiedErrorId : System.UnauthorizedAccessException,Microsoft.PowerShell.Commands.SetExecutionPolicyComma
nd
===============================
After launching Windows PowerShell as an administrator you will have more powers.
The following code listing shows how to run the command.
====
PS C:\Windows\system32> Set-ExecutionPolicy -Scope CurrentUser
cmdlet Set-ExecutionPolicy at command pipeline position 1
Supply values for the following parameters:
ExecutionPolicy: RemoteSigned
PS C:\Windows\system32>
==========================
After you type in RemoteSigned and return, you get a message from the ExecutionPolicyChange as follows:
"The execution policy helps protect you fromscripts that you do not trust. Changing the execution policy might expose you to security risks described in the about_Execution_Policies help topic at http://go.microsoft.com/fwlink/?LinkID=135170. Do you want to change the execution policy? with three ptions, yes,no and suspend.
Click Yes.
You will not get a message that the policy has been changed but it will have changed.
========
Now we run the file as shown in the next listing.
=========
PS C:\windows\system32> C:\Users\Jayaram\Desktop\Hello.ps1
Hello World
PS C:\windows\system32>
================
Finally what was the content of the 'Hello.ps1'?
It is the 'Hello World' example and the file has only the following content with just two lines typed into Notepad and saved to Desktop as 'Hello.ps1':
============
$StringToPrint="Hello World"
Write-output $StringToPrint




No comments:
Post a Comment